Just how certain are you that your username and passwords are secure?
Lets put them to the test then?
Think of a card, any card. Now, keep that card in mind and think of another. Repeat until you’ve picked twelve cards—but make sure your selection includes all four suits, at least one ace and one face card, and no two instances of the same card. Remember the whole set, because I’m going to ask you again tomorrow…
I’m joking, of course. But have you ever noticed that when magicians pull someone out of an audience to help with a trick, they never make such complicated requests? It’s not reasonable to ask someone to create a meaningless string of numbers and letters, remember it indefinitely, and produce it on demand.
But Web sites, banks, and network administrators make exactly that request of us almost daily. Want to buy something online? Sure, but you need more than a credit card—you need a password too. Sync this data with the cloud, sign up for that free service, manage your utilities or payment schedule online…no problem, but you must have a password for that.
“Make sure it’s between 10 and 14 characters, contains upper- and lowercase letters, at least one digit, at least one punctuation character, and doesn’t have any repeated strings. Oh yeah, and don’t even think about using a word that might be found in a dictionary or reusing a password you used anywhere else.”
Are you kidding me? This is madness. Coming up with unique, random passwords all the time, remembering them, and producing them reliably is not the sort of task the human brain is cut out for.


Your weakest link
Speaking as a fellow human being, I don’t blame anyone for taking the easy way out. You might try to come up with clever, random-looking passwords the first few times, but once your list of password-protected accounts grows into the dozens, and then the hundreds, it’s not plausible to keep following the rules.
However, speaking as a technologist who has spent lots of time researching and thinking about security, I’m terrified for people who do this. I know how easy it is to guess, crack, or otherwise uncover someone’s passwords because I’ve done it myself. And people with far greater skills and resources than mine spend all day, every day doing the same thing—not for legitimate security research but to steal money and secrets, to cause mischief, or to show off.
So what happens to your data.
If someone else learns your password, that person can access your data, and that’s just the beginning. Once access is granted, the “hacker” can change your password so you can’t access your own account, impersonate you online, and even change your contact data to theirs.
And, if you use the same password for other sites and services, the hacker can get access just as easily to your other accounts and wreak all kinds of havoc, up to and including “stealing” your identity. If they cant extract value from your account, they can simply leak or sell that information on in bulk
Can I check if my details have been leaked?
If you’re worried about being hacked, or feel like you may have fallen victim already, there is a number of sites where you can check if your account details are being sold online and steps you can take to avoid it.
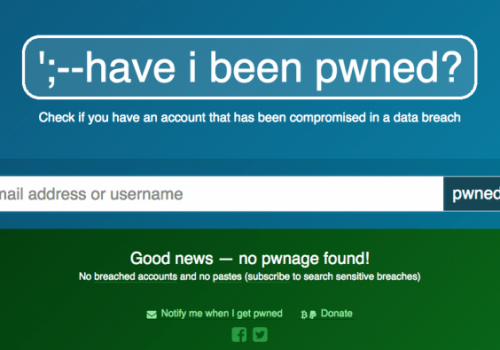
Have I Been Pwned
Set up by security researcher Troy Hunt, Have I Been Pwned? has become the go-to site for concerned web users. have I Been Pwned? catalogues all the email addresses and other data taken in high-profile breaches on his website. You can’t see the full list of addresses; instead, you can search to see if your email address is on his vast database.
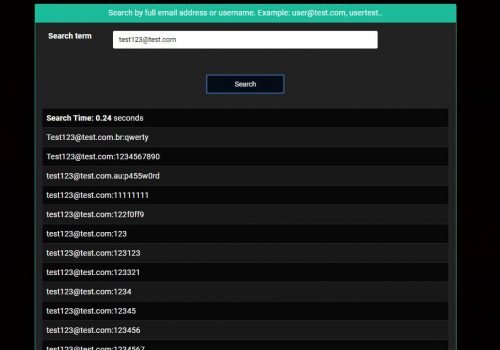
Ghostproject.Fr
Never heard of ghostproject.fr? Well, “It’s big! 1.4 Billion Clear Text Credentials Discovered in a Single Database.
Simply enter some of your email addresses and it will show you any leaked passwords….. Yes, you heard that correct, your passwords, displayed clearly to the billions of people on the internet.
OK, So what should I do…Follow these tips!
1- Please don’t use the same passwords…Please!
I want to repeat it until you believe—is that reusing passwords is a terrible, terrible idea. Just. Don’t. Ever. Do. It.
The basic argument is simple. If your password for one site or service is compromised (stolen, guessed, hacked) as per above, it may even be an old password for that matter.
However, you also used that password somewhere else, then whoever has your password might try it elsewhere and be able to do that much more damage. If you use the same password everywhere, you’re essentially handing over all your personal data and access to the first person who learns your password.
2 – Use a combination of uppercase and lowercase letters, symbols and numbers
Passwords that are as meaningless and random as possible are the hardest to crack!
3 – To make your passwords more complex, add on a simple number sequence
Once you have your phrase, make your password harder by adding 3 or 4 numbers. Think of a combination that only you know and add that onto all your passwords, e.g “LiveAndLetDie007.”
4 – Change your password regularly, at least every 3 months
Make sure not to reuse any old passwords. To make them easier to remember, try adding the month and year at the end and update it every couple of months. You’ll also be aware of how old the password is as well this way!
5 – Consider using a password manager.
If you have too many passwords to remember, rather than writing them down, use a password manager that encrypts and stores your passwords for you! These systems secure all your passwords safely for you, they enter them automatically for you, and you only have to remember one master password to access the programme.
Isn’t a password manager putting all my eggs in one basket?
Unsurprisingly, password managers take security very seriously (it’s why they exist, after all). At the risk of getting technical, they typically use strong ‘256-bit Advanced Encryption Standard’ encryption to make reading your data very difficult, among other measures. Some password managers also use ‘two factor-authentication’, whereby a second login step using a different device is required (eg, you may be texted a code to enter online).
Having said that, no solution is ever 100% secure and it’s always possible a password manager itself could be hacked (though if it was, the hackers would still have to decrypt your data). At the end of the day, they’re more secure than the vast majority of websites.
6 – Turn on two-factor authentication (2FA)
To secure any online account even further, you can turn on an extra layer of protection called two-factor authentication (2FA). 2FA is a way for the service you’re using to double check that you really are the person you claim to be when logging in. For example, by sending a security code to your mobile phone. This ensures that any cyber-criminals in possession of your password still can’t access your account because they won’t have this “second factor”.
More from our blog
Follow Us
Based In Keele, SyTech IT provide IT Solutions, Support & Systems for Industry and multi channel distribution businesses within Stoke-on-Trent, Staffordshire, Derbyshire, Cheshire, Lancashire, Warwickshire, Birmingham and Manchester.